The Internet of Things
This week, a news story broke that left everyone stunned—the level of surprise seemed to depend on how much we know about the Internet.
So, to clear things up and help us make sense of the story, let’s break down a few key points.
“Last Friday, October 21st, a DDoS attack took down Dyn, which in turn disrupted dozens of websites, services, and several social networks such as Amazon, Reddit, Github, Spotify, and more. The attack exploited vulnerabilities in millions of connected accessories, devices, and appliances.”
“The attack could have been carried out by people with little technical knowledge, and as of today, there’s nothing we can do about it.”
“This individual or group used botnets, leveraging Mirai to probe the vulnerabilities in device firmware and operating systems.”
These three paragraphs sum up the story that serves as the basis for this post.
First, let’s break them down to identify the key takeaways.
- It’s shocking how vulnerable even major companies are.
- You don’t need to work at a particle accelerator to take on a giant.
- What are botnets? Are they the new weapon of mass destruction?
- This feels straight out of a Terminator movie.
- What exactly is the Internet of Things?
There’s nothing more tempting for a hacker than ruining the day for a corporate giant—especially if it means making headlines and getting TV coverage.
So, the main motivation here is fame.
To achieve it, all they need to do is use botnets to flood the targeted websites with requests.
Botnets?
Yes, botnets—the new digital warriors. They don’t tire, they don’t eat, and they barely use up any ammo.
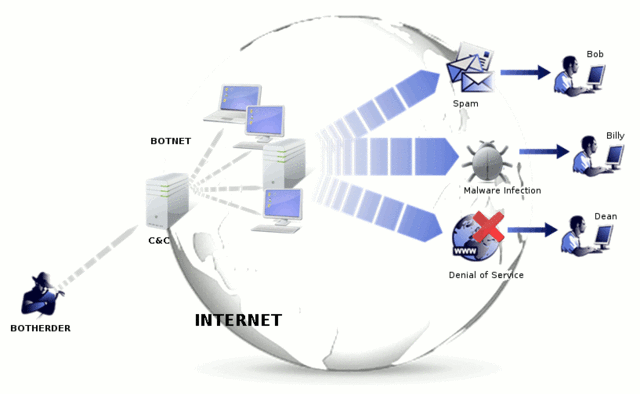
A botnet is a network of computers or devices running automated software robots. The botnet creator remotely controls all infected computers or servers.
From the comfort of their armchair, the creator programs these botnets to infiltrate our computers and, once inside, use them like mind-controlling parasites. The trick is, we don’t even notice.
Let’s say someone builds a botnet for malicious purposes. The first step is to infect millions of computers worldwide. Once that’s done, the next step is to command the bots to do whatever the creator wants.
Servers are simple in principle—they store our websites and deliver them when we request them.
A request can be as simple as visiting the JordiEnsenyatDisseny website to ask for more information. Signing up for your favorite museum’s newsletter is also a request.
When these requests happen organically, there’s usually no problem—server capacity is planned based on typical human usage.
But if millions of computers around the world make requests at the same time, it’s a different story. That’s why bots are used. One person with bad intentions can wield the power of millions through botnets.
To avoid becoming part of this, it’s as simple as installing a good antivirus and, ideally, a malware detection program—essential to keep your computer from joining a zombie network.
By 2020, the number of connected devices is estimated to reach between 22 and 50 billion!
But what’s remarkable about this attack is that it was carried out through the Internet of Things.
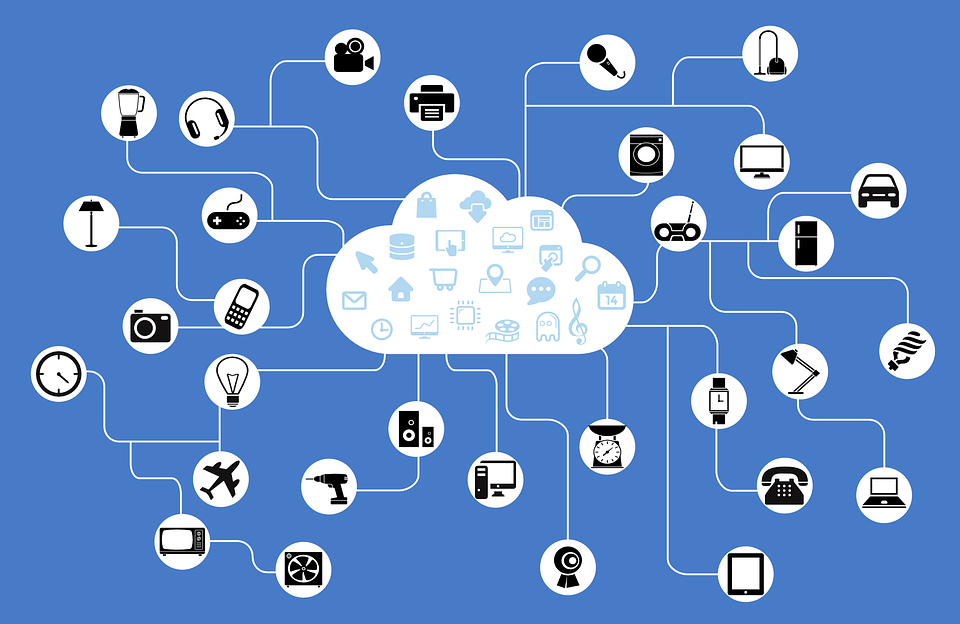
The Internet of Things refers to all those everyday devices that are now connected to the Internet.
Today, there are countless products on the market with Wi-Fi and Internet connectivity.
Refrigerators that notify you when food is about to expire, sneakers that upload your stats to the cloud, smart toys for kids…
These devices have huge potential, but very little protection against malware attacks. They’re a double-edged sword.
That’s how the attack happened: the Wi-Fi of millions of infected video cameras was used to overwhelm Dyn’s network via Mirai.